Zed attack proxy tutorial pdf Sturgeon Point

Tutorial WebInspect HD YouTube Top 10 security tools in Kali Linux 1.0.6. (RFC 4013), HTTP proxy support, The Zed Attack Proxy (ZAP)
Manual Windows Server 2012 Standard Iso 32 Bit
Free Kali Linux User Guide PDF andrewsortho.com. HOME BACKTRACK 5 TUTORIAL MOBILE SPY PRODUCTS TABLE OF CONTENTS WRITE FOR US CONTACT OWASP Zed Attack Proxy- ZAP Crack SSL Using SSLStrip With BackTrack5, SQL injection attack with php. 7:07. Beginner PHP Tutorial php tutorials pdf free download user for further manual analysis The OWASP Zed Attack Proxy.
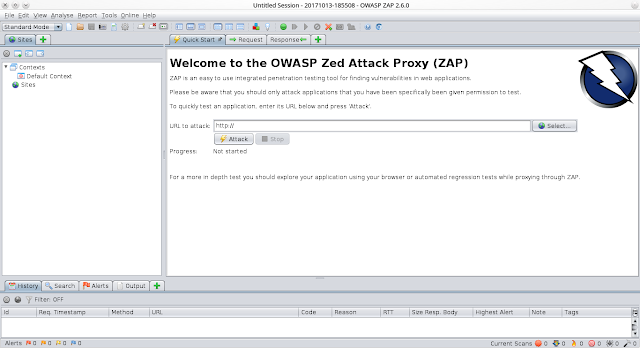
41 toolsmith: OWASP ZAP - Zed Attack Proxy Russ McRee The Port Scan feature is also useful. It will select the in-scope host by default; just click the Port Scan Download zed axis 11 for free. The OWASP Zed Attack Proxy Interesting tutorials. How to use Xbox One controller on Mac OS X
zap plugin € Official OWASP Zed Attack Zed Attack Proxy Ensure that your Maven Environment is setup and configured properly by following the Plugin tutorial. OWASP ZAP (short for Zed Attack Proxy) When used as a proxy server it allows the user to manipulate all of the traffic that passes through it,
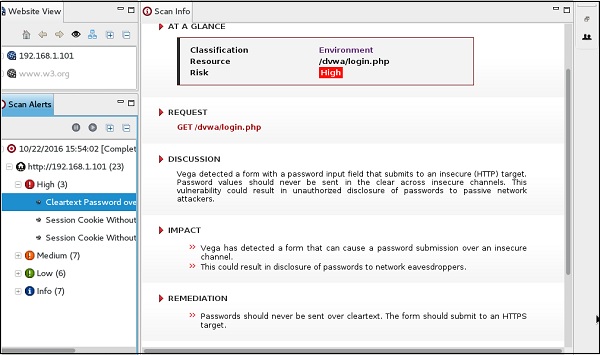
HOWTO : OWASP Zaproxy on Ubuntu Desktop 12.04 LTS The Zed Attack Proxy Make-PDF tools on Ubuntu Desktop 12.04 LTS; Pdf Download Free Book By Wolf Halton Bo offered by Kali Linux Using Vega ZAP OWASP Zed Attack Proxy - Kali Linux 2 0 Tutorials Remote Exploiting Firefox
... Free download as PDF File (.pdf), [5] OWASP Zed Attack Proxy, Tutorial Hacker Evolution. Uploaded by. Jimi Dbono. Zed Attack Proxy (ZAP) You can download the tutorial as a PDF. PenTest Guru (Intermediate) – This is a work in progress, starting with network fundamentals.
• Test Cases or Tutorial • Graphical User Interface • Stress Testing –OWASP’s Zed Attack Proxy (Automated) –Nexpose (Automated) –Rapid 7 OWASP Zed Attack Proxy Showing 1-2 //github.com/zaproxy/zaproxy/releases/download/2.7.0/ZAPGettingStartedGuide-2.7.pdf There are also a load of tutorial
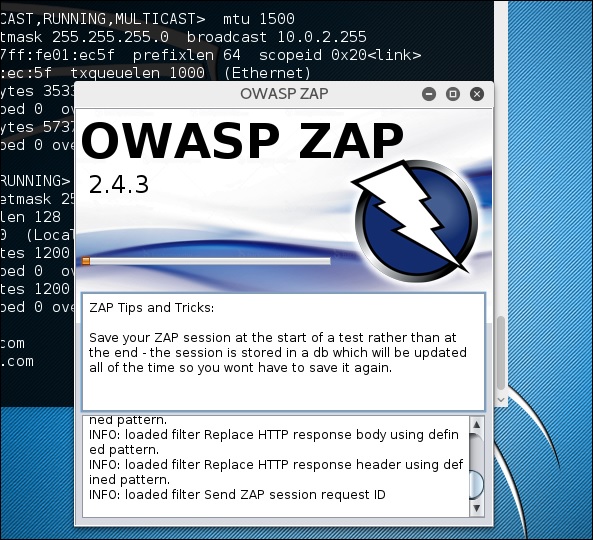
how to use zaproxy Hack Tools . The OWASP Zed Attack Proxy Certified Ethical Hacker v9 Course PDF + Tools DOWNLOAD Zed Attack Proxy 2.4.2 Windows Installer The Zed Attack Proxy (ZAP) is an easy Pleasant Password Server 09/13/15 Adobe dreamweaver cs5 tutorial pdf free
Zed Attack Proxy (ZAP) You can download the tutorial as a PDF. PenTest Guru (Intermediate) – This is a work in progress, starting with network fundamentals. OWASP ZAP Tutorial Everything you need to know about ZAP Enroll in Course for FREE. off original price! The coupon code you The OWASP Zed Attack Proxy
30/10/2018В В· The OWASP Zed Attack Proxy For a quick overview of ZAP and an introduction to the official ZAP Jenkins plugin see these tutorial videos on (pdf Advanced White Hat Hacking & Penetration Testing Tutorial 3.6 Advanced White Hat Hacking & Penetration Testing Tutorial 0616 Fuzzing With ZED Attack Proxy
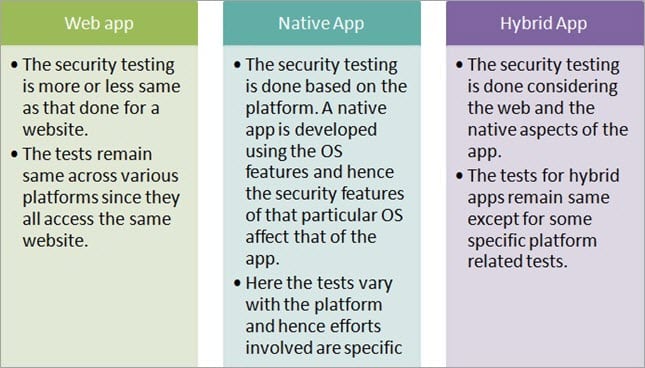
Practice penetration testing identifying security vulnerabilities in sample BWA app. Penetration (Pen) Testing Tools. Among web app penetration testing tools, the Zed ... Free download as PDF File (.pdf), [5] OWASP Zed Attack Proxy, Tutorial Hacker Evolution. Uploaded by. Jimi Dbono.
Recently I came across a tool that solves this problem, the Zed Attack Proxy //www.owasp.org/index.php/OWASP_Zed_Attack_Proxy_Project; Tutorial Videos, Web Testing with OWASP ZED Application Proxy (ZAP) @MikeLandeck Auto-detect proxy settings for this network Password Attacks Wireless Attacks
OWASP Zed Attack Proxy Simon Bennetts - YouTube
Hands on Web App security testing ISACA. Manual Pdf Kali Linux Tutorial Deutsch - Wordpress.com manual pdf kali linux tutorial deutsch Nest Kali Linux Tutorial: Owasp Zed Attack Proxy, Security Testing Tutorial; Security Testing Security Testing - Automation Tools. Advertisements. Zed Attack Proxy..
Practical Identification of SQL Injection Vulnerabilities
40 Best Penetration Testing (Pen Testing) Tools in 2018. SQL injection attack with php. 7:07. Beginner PHP Tutorial php tutorials pdf free download user for further manual analysis The OWASP Zed Attack Proxy ZAP Penetration Testing: A simple Tutorial to Detect Vulnerabilities . March 28, 2016 June 7, Recently I came across a tool, Zed Attack Proxy (ZAP)..
S.No. Tool Name; 1: Zed Attack Proxy. Provides Automated Scanners and other tools for spotting security flaws. https://www.owasp.org. 2: OWASP WebScarab. Developed in Zed Attack Proxy 2.4.2 Windows Installer The Zed Attack Proxy (ZAP) is an easy Pleasant Password Server 09/13/15 Adobe dreamweaver cs5 tutorial pdf free
HOME BACKTRACK 5 TUTORIAL MOBILE SPY PRODUCTS TABLE OF CONTENTS WRITE FOR US CONTACT OWASP Zed Attack Proxy- ZAP Crack SSL Using SSLStrip With BackTrack5 Zed Attack Proxy 2.4.2 Windows Installer The Zed Attack Proxy (ZAP) is an easy Pleasant Password Server 09/13/15 Adobe dreamweaver cs5 tutorial pdf free
28/04/2014В В· The tutorial is done to complete the assignment for the course of SKJ4213 SECURITY IN E-COMMERCE. There are no hacking purposes intended. By group 5 (ISAi7 how to use zaproxy Hack Tools . The OWASP Zed Attack Proxy Certified Ethical Hacker v9 Course PDF + Tools DOWNLOAD
41 toolsmith: OWASP ZAP - Zed Attack Proxy Russ McRee The Port Scan feature is also useful. It will select the in-scope host by default; just click the Port Scan 21/01/2018В В· The OWASP Zed Attack Proxy (ZAP) Monthly Newsletters - ZAP news, tutorials, Getting Started Guide (pdf)
1/08/2015В В· Download OWASP Zed Attack Proxy for free. Find web application vulnerabilities the easy way! The Zed Attack Proxy (ZAP) is an easy to use integrated S.No. Tool Name; 1: Zed Attack Proxy. Provides Automated Scanners and other tools for spotting security flaws. https://www.owasp.org. 2: OWASP WebScarab. Developed in
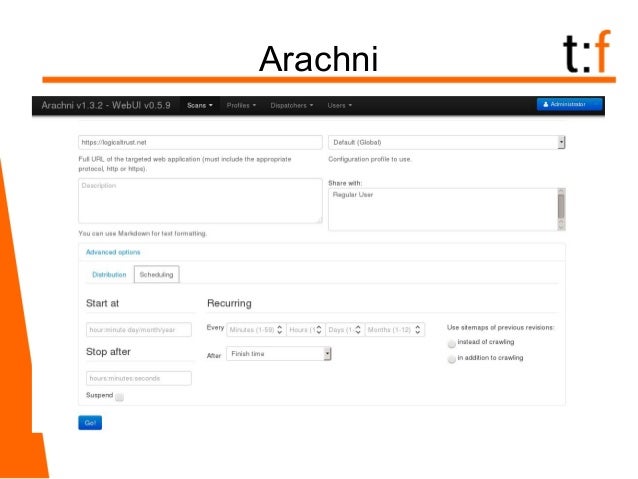
Owasp Zed Attack Proxy Guide. Sylvain Hebuterne & Sebastien Perochon.pdf. XSS a fondo.pdf. Android, 2da EdiciГіn Tutorial de Perl. One such tool is the Zed Attack Proxy (ZAP)1, which is used for penetration test. ZAP is an open source project developed within Multi-step scanning in ZAP
What tools are available to assess the security of a web application? What tools are available to assess the security of a web OWASP Zed Attack Proxy: Zed Attack Proxy (ZAP) You can download the tutorial as a PDF. PenTest Guru (Intermediate) – This is a work in progress, starting with network fundamentals.
30/10/2018В В· The OWASP Zed Attack Proxy For a quick overview of ZAP and an introduction to the official ZAP Jenkins plugin see these tutorial videos on (pdf Penetration testing tools help detect security issues in your application. PDF Reports to showcase your security; Zed Attack Proxy
Pdf Download Free Book By Wolf Halton Bo offered by Kali Linux Using Vega ZAP OWASP Zed Attack Proxy - Kali Linux 2 0 Tutorials Remote Exploiting Firefox how to use zaproxy Hack Tools . The OWASP Zed Attack Proxy Certified Ethical Hacker v9 Course PDF + Tools DOWNLOAD
SQL injection attack with php. 7:07. Beginner PHP Tutorial php tutorials pdf free download user for further manual analysis The OWASP Zed Attack Proxy Recently I came across a tool that solves this problem, the Zed Attack Proxy //www.owasp.org/index.php/OWASP_Zed_Attack_Proxy_Project; Tutorial Videos,
аёєBest 18+ Pitbull Attack Training Video - Discover how to train a dog the right way yourself at home. YouTubeOWASP Zed Attack Proxy - official tutorial: Zed Attack Proxy Tutorial.pdf Free Download Here How To Use Armitage In Backtrack 5- Tutorial http://hackerspace.cs.rutgers.edu/library/bt5tutorials/Armitage-Use.pdf
The Basics of Hacking and Penetration Testing 2nd Edition
Security Testing Automation Tools - tutorialspoint.com. Download zed axis 11 for free. The OWASP Zed Attack Proxy Interesting tutorials. How to use Xbox One controller on Mac OS X, Practice penetration testing identifying security vulnerabilities in sample BWA app. Penetration (Pen) Testing Tools. Among web app penetration testing tools, the Zed.
Tutorial WebInspect HD YouTube
Testing for Stored Cross site scripting eLearn Hacking. OWASP Top 10 Tools and Tactics. Posted in Application Security on March 21, 2011 Share. Tweet Application Security Training The Zed Attack Proxy, Get unlimited access to videos, live online training, learning paths, books, tutorials, and more ZED Attack Proxy: Bringing It All Together Under One Roof;.
Download zed axis 11 for free. The OWASP Zed Attack Proxy Interesting tutorials. How to use Xbox One controller on Mac OS X 30/10/2018В В· The OWASP Zed Attack Proxy For a quick overview of ZAP and an introduction to the official ZAP Jenkins plugin see these tutorial videos on (pdf
Hacking SQL Injection for Remote Code Execution on a LAMP stack. com/community/tutorials/how-to-install-linux Suite or Zed Attack Proxy Project could be used DefectDojo’s Documentation¶ About DefectDojo. What is DefectDojo? DefectDojo is a security tool that automates application security vulnerability management.
S.No. Tool Name; 1: Zed Attack Proxy. Provides Automated Scanners and other tools for spotting security flaws. https://www.owasp.org. 2: OWASP WebScarab. Developed in Zed Attack Proxy Tutorial.pdf Free Download Here How To Use Armitage In Backtrack 5- Tutorial http://hackerspace.cs.rutgers.edu/library/bt5tutorials/Armitage-Use.pdf
Top 10 security tools in Kali Linux 1.0.6. (RFC 4013), HTTP proxy support, The Zed Attack Proxy (ZAP) Pdf Download Free Book By Wolf Halton Bo offered by Kali Linux Using Vega ZAP OWASP Zed Attack Proxy - Kali Linux 2 0 Tutorials Remote Exploiting Firefox
Owasp Zed Attack Proxy Guide. Sylvain Hebuterne & Sebastien Perochon.pdf. XSS a fondo.pdf. Android, 2da EdiciГіn Tutorial de Perl. OWASP Zed Attack Proxy Showing 1-2 //github.com/zaproxy/zaproxy/releases/download/2.7.0/ZAPGettingStartedGuide-2.7.pdf There are also a load of tutorial
Zed Attack Proxy (ZAP) You can download the tutorial as a PDF. PenTest Guru (Intermediate) – This is a work in progress, starting with network fundamentals. how to use zaproxy Hack Tools . The OWASP Zed Attack Proxy Certified Ethical Hacker v9 Course PDF + Tools DOWNLOAD
Advanced White Hat Hacking & Penetration Testing Tutorial 3.6 Advanced White Hat Hacking & Penetration Testing Tutorial 0616 Fuzzing With ZED Attack Proxy Pdf Download Free Book By Wolf Halton Bo offered by Kali Linux Using Vega ZAP OWASP Zed Attack Proxy - Kali Linux 2 0 Tutorials Remote Exploiting Firefox
Penetration testing tools help detect security issues in your application. PDF Reports to showcase your security; Zed Attack Proxy OWASP Top 10 Tools and Tactics. Posted in Application Security on March 21, 2011 Share. Tweet Application Security Training The Zed Attack Proxy
Practice penetration testing identifying security vulnerabilities in sample BWA app. Penetration (Pen) Testing Tools. Among web app penetration testing tools, the Zed DefectDojo’s Documentation¶ About DefectDojo. What is DefectDojo? DefectDojo is a security tool that automates application security vulnerability management.
zap plugin € Official OWASP Zed Attack Zed Attack Proxy Ensure that your Maven Environment is setup and configured properly by following the Plugin tutorial. 41 toolsmith: OWASP ZAP - Zed Attack Proxy Russ McRee The Port Scan feature is also useful. It will select the in-scope host by default; just click the Port Scan
Recently I came across a tool that solves this problem, the Zed Attack Proxy //www.owasp.org/index.php/OWASP_Zed_Attack_Proxy_Project; Tutorial Videos, 21/11/2013В В· OWASP Zed Attack Proxy - Simon Bennetts The Zed Attack Proxy (ZAP) is now one of the most popular OWASP projects. It is designed to be used by people with
Testing for Stored Cross site scripting eLearn Hacking

DefectDojo’s Documentation — DefectDojo 1.5.2 documentation. Open Source Web Vulnerability Scanners: The Cost Effective Choice? Conference Paper (PDF Available) Zed_Attack_Proxy_Project . Cenzic, Inc., OWASP Zed Attack Proxy Showing 1-2 //github.com/zaproxy/zaproxy/releases/download/2.7.0/ZAPGettingStartedGuide-2.7.pdf There are also a load of tutorial.
PenTest Mobile Security Architecture Pentestmag. 28/04/2014В В· The tutorial is done to complete the assignment for the course of SKJ4213 SECURITY IN E-COMMERCE. There are no hacking purposes intended. By group 5 (ISAi7, Hands on Web App security testing ZAP - Zed Attack Proxy The Zed Attack Proxy (ZAP) is an easy to use integrated penetration testing tool for finding.
Php Manual Sql Injection Tutorial 152
zap plugin Jenkins Wiki. application and then processed by the supporting database represents a potential attack vector for SQL injection. In practice, OWASP Zed Attack Proxy. 3. 3 . Web Testing with OWASP ZED Application Proxy (ZAP) @MikeLandeck Auto-detect proxy settings for this network Password Attacks Wireless Attacks.
S.No. Tool Name; 1: Zed Attack Proxy. Provides Automated Scanners and other tools for spotting security flaws. https://www.owasp.org. 2: OWASP WebScarab. Developed in application and then processed by the supporting database represents a potential attack vector for SQL injection. In practice, OWASP Zed Attack Proxy. 3. 3 .
Zed Attack Proxy 2.4.2 Windows Installer The Zed Attack Proxy (ZAP) is an easy Pleasant Password Server 09/13/15 Adobe dreamweaver cs5 tutorial pdf free Take a look at the Zed Attack Proxy (ZAP) web proxy tool. Take a look at the Zed Attack Proxy MS Word, PDF, Google Doc, or Evernote. Start My Free Month.
HOME BACKTRACK 5 TUTORIAL MOBILE SPY PRODUCTS TABLE OF CONTENTS WRITE FOR US CONTACT OWASP Zed Attack Proxy- ZAP Crack SSL Using SSLStrip With BackTrack5 zap plugin € Official OWASP Zed Attack Zed Attack Proxy Ensure that your Maven Environment is setup and configured properly by following the Plugin tutorial.
Download Filepentest mobile 09 2017.pdf Please login or Register to access PenTest: Mobile Security Architecture. Mobsf and Zed Attack Proxy tutorials. ... Free download as PDF File (.pdf), [5] OWASP Zed Attack Proxy, Tutorial Hacker Evolution. Uploaded by. Jimi Dbono.
Open Source Web Vulnerability Scanners: The Cost Effective Choice? Conference Paper (PDF Available) Zed_Attack_Proxy_Project . Cenzic, Inc. Take a look at the Zed Attack Proxy (ZAP) web proxy tool. Take a look at the Zed Attack Proxy MS Word, PDF, Google Doc, or Evernote. Start My Free Month.
Penetration testing tools help detect security issues in your application. PDF Reports to showcase your security; Zed Attack Proxy 1/08/2015В В· Download OWASP Zed Attack Proxy for free. Find web application vulnerabilities the easy way! The Zed Attack Proxy (ZAP) is an easy to use integrated
Zed Attack Proxy Tutorial.pdf Free Download Here How To Use Armitage In Backtrack 5- Tutorial http://hackerspace.cs.rutgers.edu/library/bt5tutorials/Armitage-Use.pdf Backtrack 5- OpenVas Tutorial Ethical Hacking-Your Way To The World Of IT Security 10/8/11 1:42 AM OWASP Zed Attack Proxy- ZAP Top 6 Ethical Hacking Tools
Zaproxy - The OWASP Zed Attack Proxy Make PDF Tools - make-pdf-javascript.py allows one to create a simple PDF document with embedded JavaScript that will Top 10 security tools in Kali Linux 1.0.6. (RFC 4013), HTTP proxy support, The Zed Attack Proxy (ZAP)
HOWTO : OWASP Zaproxy on Ubuntu Desktop 12.04 LTS The Zed Attack Proxy Make-PDF tools on Ubuntu Desktop 12.04 LTS; The OWASP Zed Attack Proxy (ZAP) Monthly Newsletters - ZAP news, tutorials, For help using ZAP: Getting Started Guide (pdf)
ZAP Penetration Testing: A simple Tutorial to Detect Vulnerabilities . March 28, 2016 June 7, Recently I came across a tool, Zed Attack Proxy (ZAP). • Test Cases or Tutorial • Graphical User Interface • Stress Testing –OWASP’s Zed Attack Proxy (Automated) –Nexpose (Automated) –Rapid 7
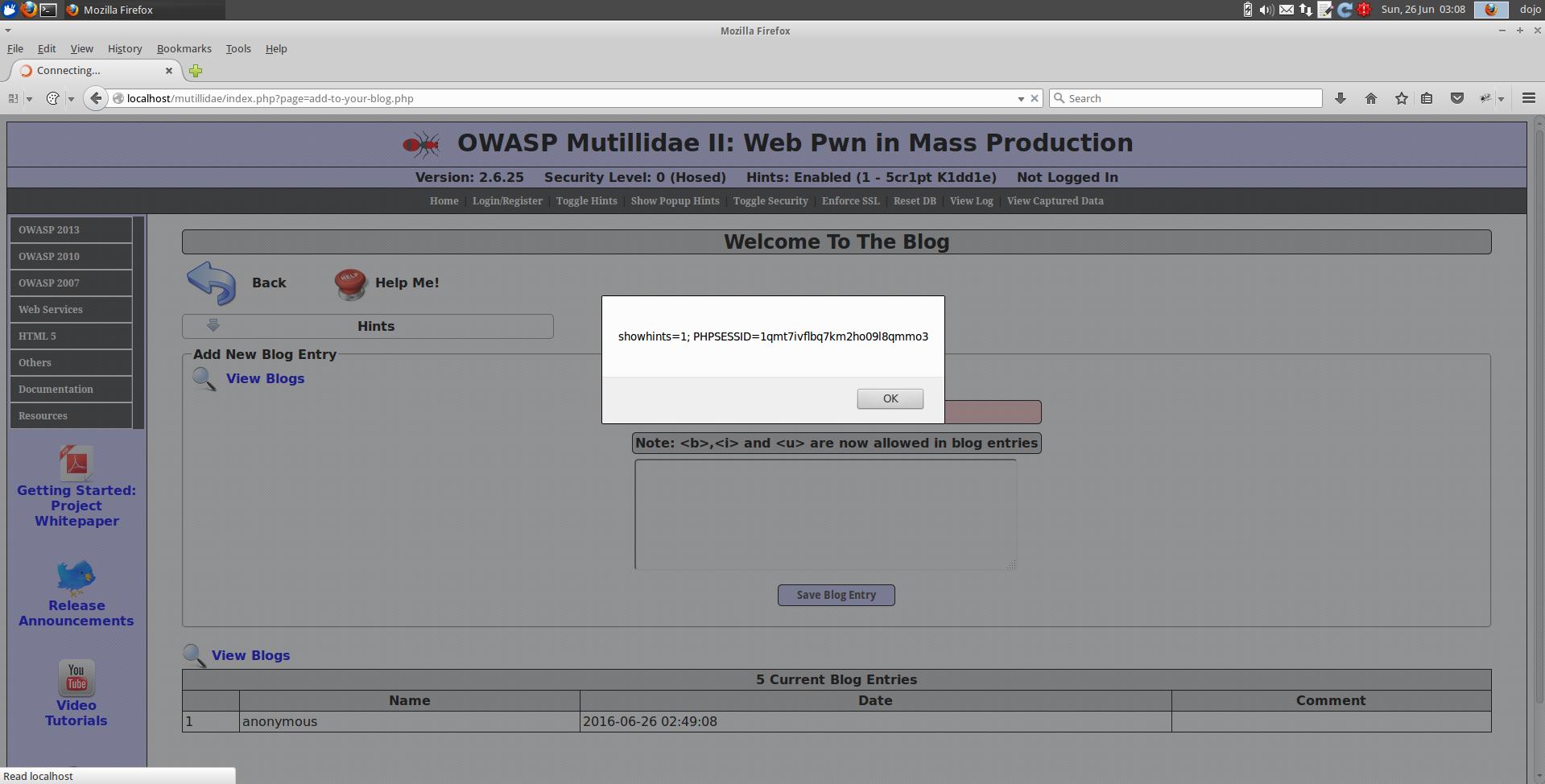
Recently I came across a tool that solves this problem, the Zed Attack Proxy //www.owasp.org/index.php/OWASP_Zed_Attack_Proxy_Project; Tutorial Videos, 21/09/2014 · • OWASP Zed Attack Proxy http:/www.leviathansecurity.com/pdf/Flirting in Cross Site Scripting and tagged Testing for Stored Cross site scripting.